Guides View More
Blockchain Smart Contract, What Is It?
Just like other contracts, smart contracts involve terms of deals or agreements. However, those terms are created and executed as codes run on the blockchain…
Simplified Guide to Blockchain Wallet Best Practices
Bitcoin, Ethereum, and other cryptocurrencies have become more popular because of their improvements over the traditional financial system. Anyone who wants to use a blockchain-based…
Your Guide to Blockchain Technology Trends You Should Check Out Before 2022 Ends
Many people assume that blockchain is simple a cryptocurrencies foundation. However, this innovation is more than that. One of the significant developments of the 21st…
Ripple: The Complete Guide
Ethereum and Bitcoin are leading the way in the world of cryptocurrency- the digital coins which occupy first and second positions in market capitalization. On…
What Is A Public Blockchain? Beginner’s Guide
What is meant by public blockchain, and how does it work? What makes it apart from the private blockchain? In what specific cases do I…
Celebrity Net Worth View More
Will Smith Net Worth
Will Smith, the iconic actor, musician, and entrepreneur, has amassed considerable wealth over the years, branching out far beyond the entertainment sector. This article provides…
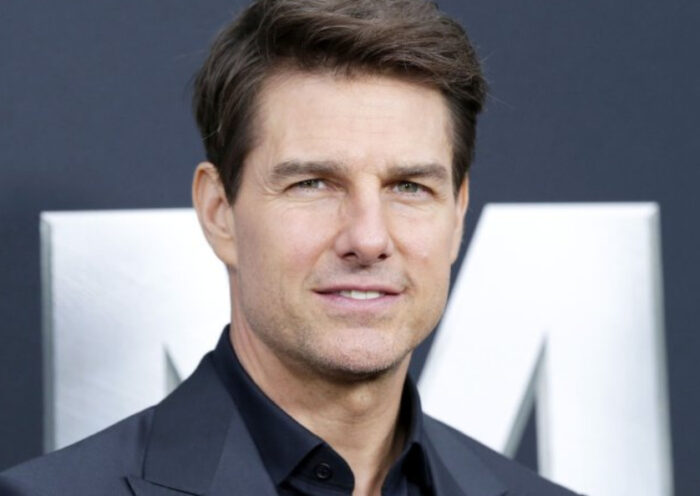
Tom Cruise Net Worth
Tom Cruise, one of Hollywood’s most iconic actors, has amassed a fortune over his illustrious career. Beyond his movie earnings, Cruise’s financial portfolio includes diverse…
Beyonce Net Worth
Beyonce, an international music icon, has not only impacted the music world but also the financial one. Beyond her chart-topping albums and tours, she has…
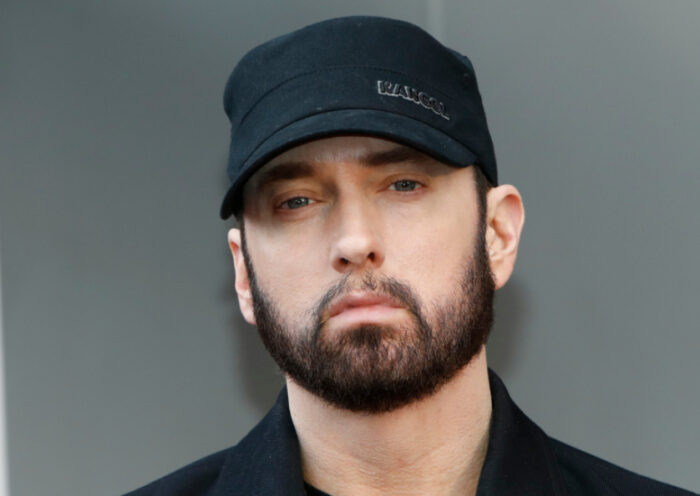
Eminem Net Worth
Eminem, a renowned rap artist known globally for his music and brand, has built a formidable financial portfolio over the years. Born as Marshall Mathers,…
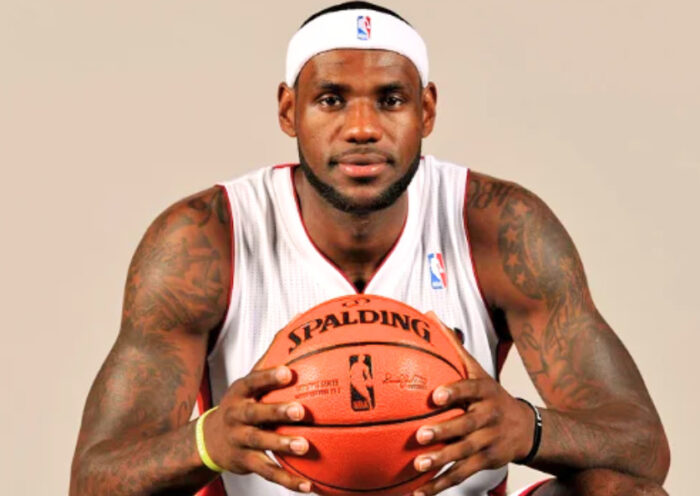
LeBron James Net Worth
LeBron James, renowned as one of the greatest basketball players of all time, has expanded his horizons beyond the basketball court. Over the years, LeBron…